MITRE ATT&CK™ Analysis - T1546.001 Change Default File Association
Change Default File Association
Whenever a file is opened in Windows the operating system checks the file association of that file type/extension against a list of known utilities setup to run that program. For example a .doc file may open in MS Word, a .jpeg an image viewer, a .txt notepad and so on. By modifying these association values in the registry, we are able to call an arbitrary program when a file with the given extension is opened.
Change Default File Association Analysis
Lab Example
RED TEAM: ATTACK
In the below example we have gone ahead and created our very own file extension ‘.raiju’. Within this we have set the default command to run as calc.exe whenever a ‘.raiju’ file is opened. We have also placed an enticing file called YummyBurgers.raiju on the desktop which is nothing more than a null byte file.
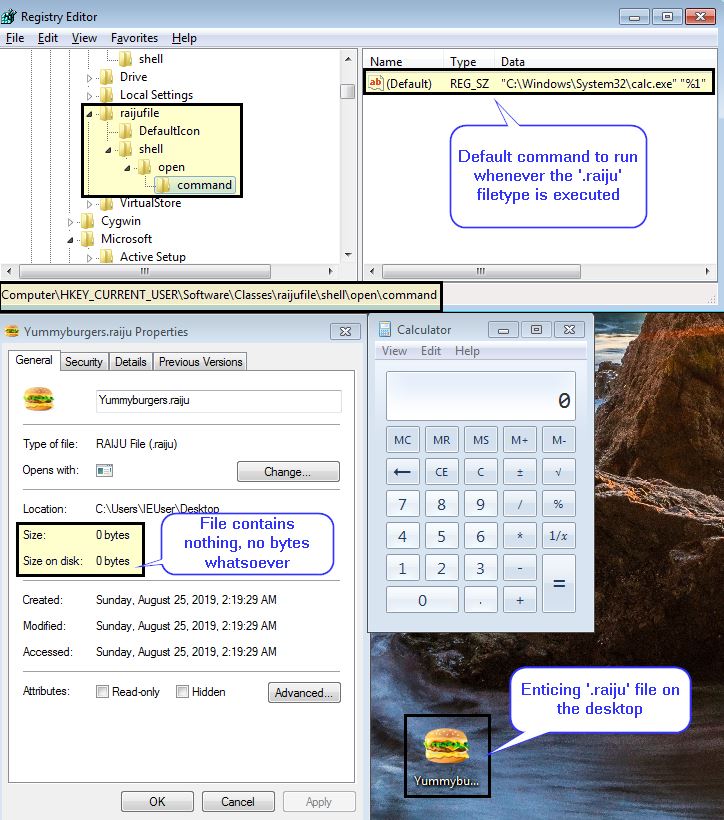
By running this blank file we spawn calc.exe on this host which can be an excellent way of maintaining persistence.
BLUE TEAM: DEFEND
This abuses system features so isn’t easily detectable; however, we can see through Sysmon that event type 13 reveals this to us.
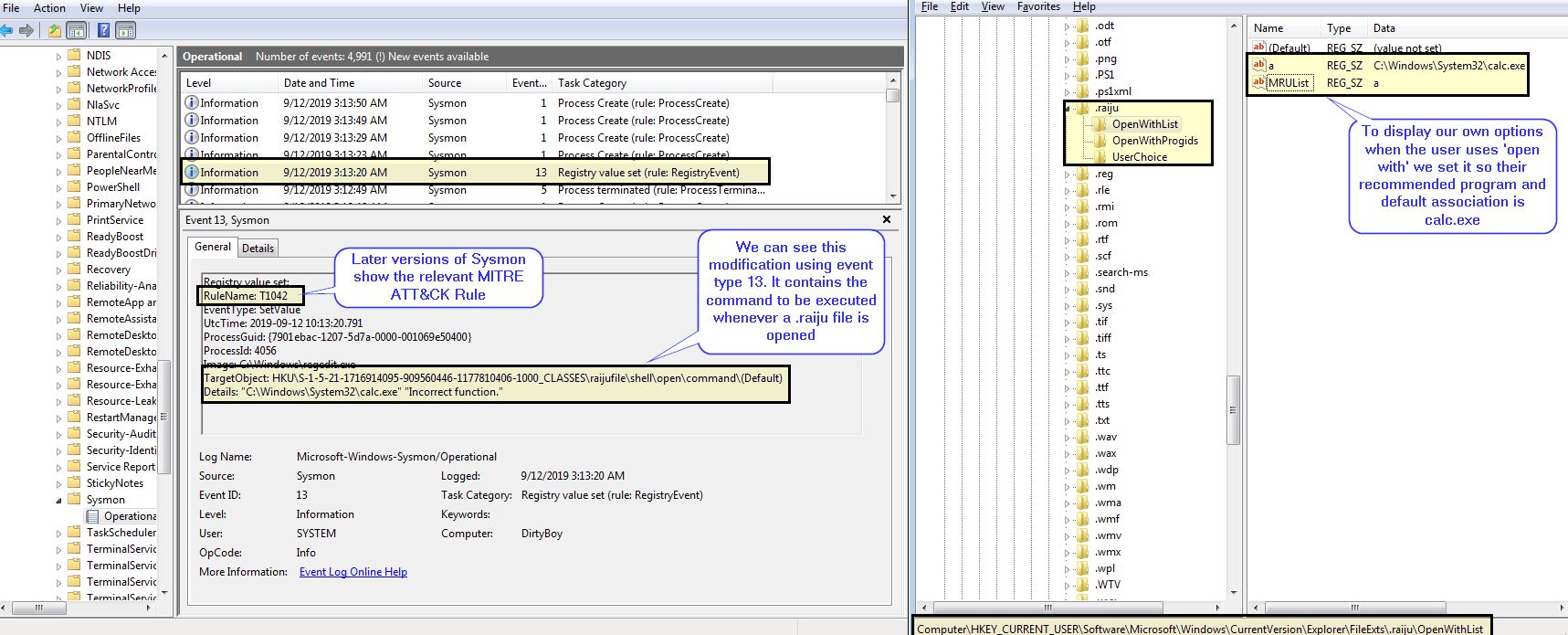
*Clarification - later versions of Sysmon allow us to define a rule name. This has been used as a way of mapping this to the MITRE Technique in our Sysmon configuration.
The end result is that we have a null byte file which essentially acts as a bootstrapper to execute ‘malware’ on this machine.




