MITRE ATT&CK™ Analysis
Overview
For those who don’t know, ATT&CK was created by the team at MITRE and stands for Adversary Tactics, Techniques, and Common Knowledge. This is widely becoming the most used common language for both offensive and defensive teams when it comes to discussing an attack vector and what specific actions are involved in exploiting that attack vector.
MITRE ATT&CK™ Analysis
This section aims to document various tests I’ve run using MITRE ATT&CK techniques, how they are used, and some supporting information on how they can be detected, mitigated, or prevented.
Old: The current progress of completion here compared to the techniques noted by MITRE can be seen visually using a custom JSON file overlayed to their Attack Navigator
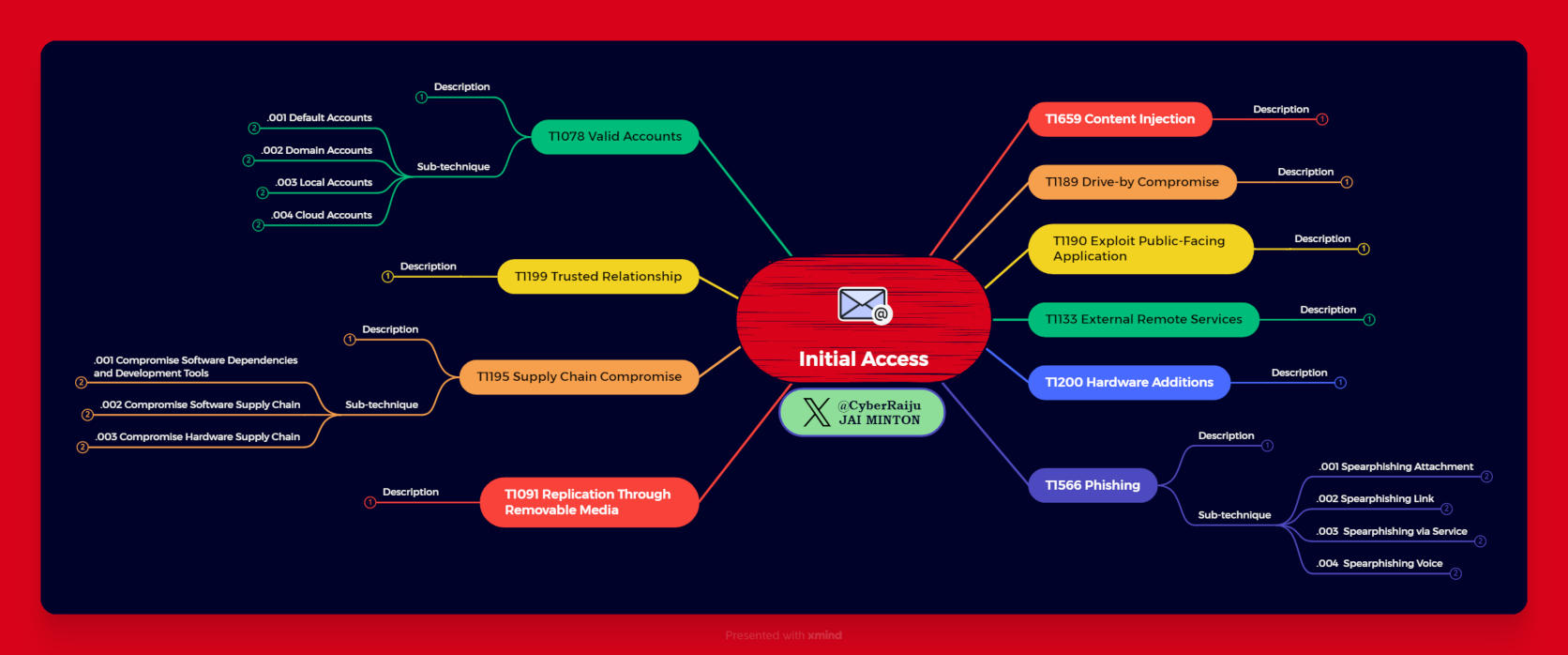
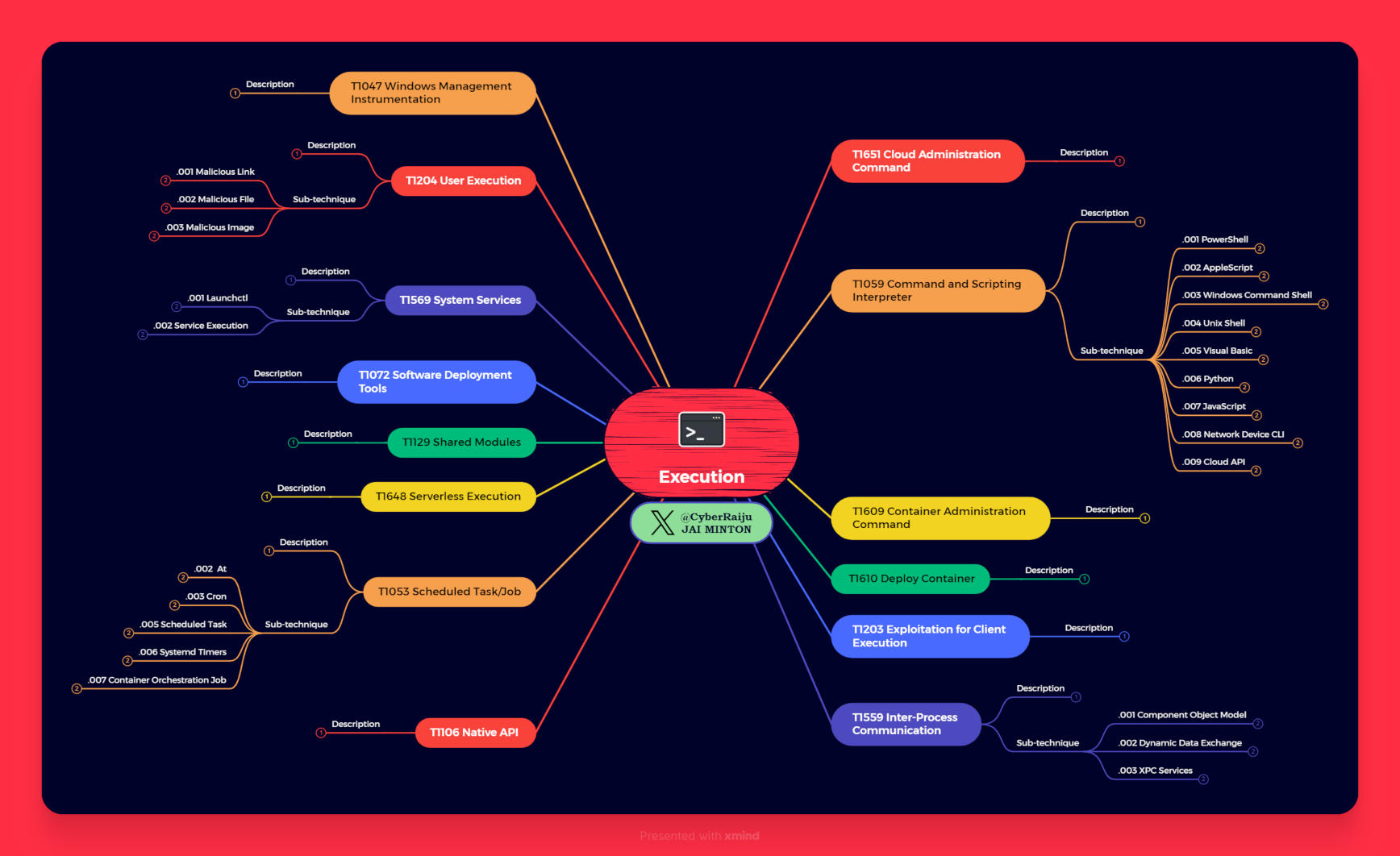
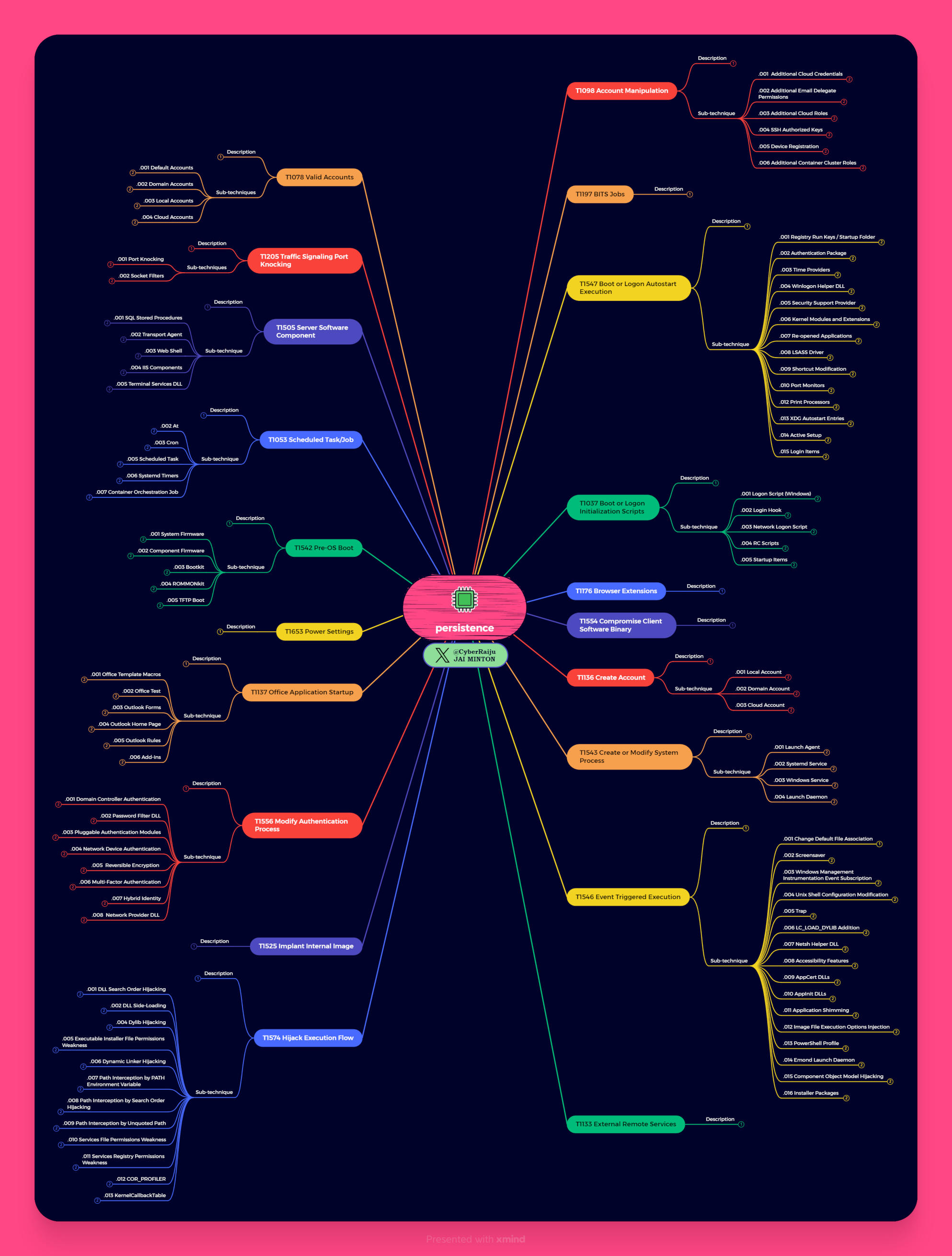
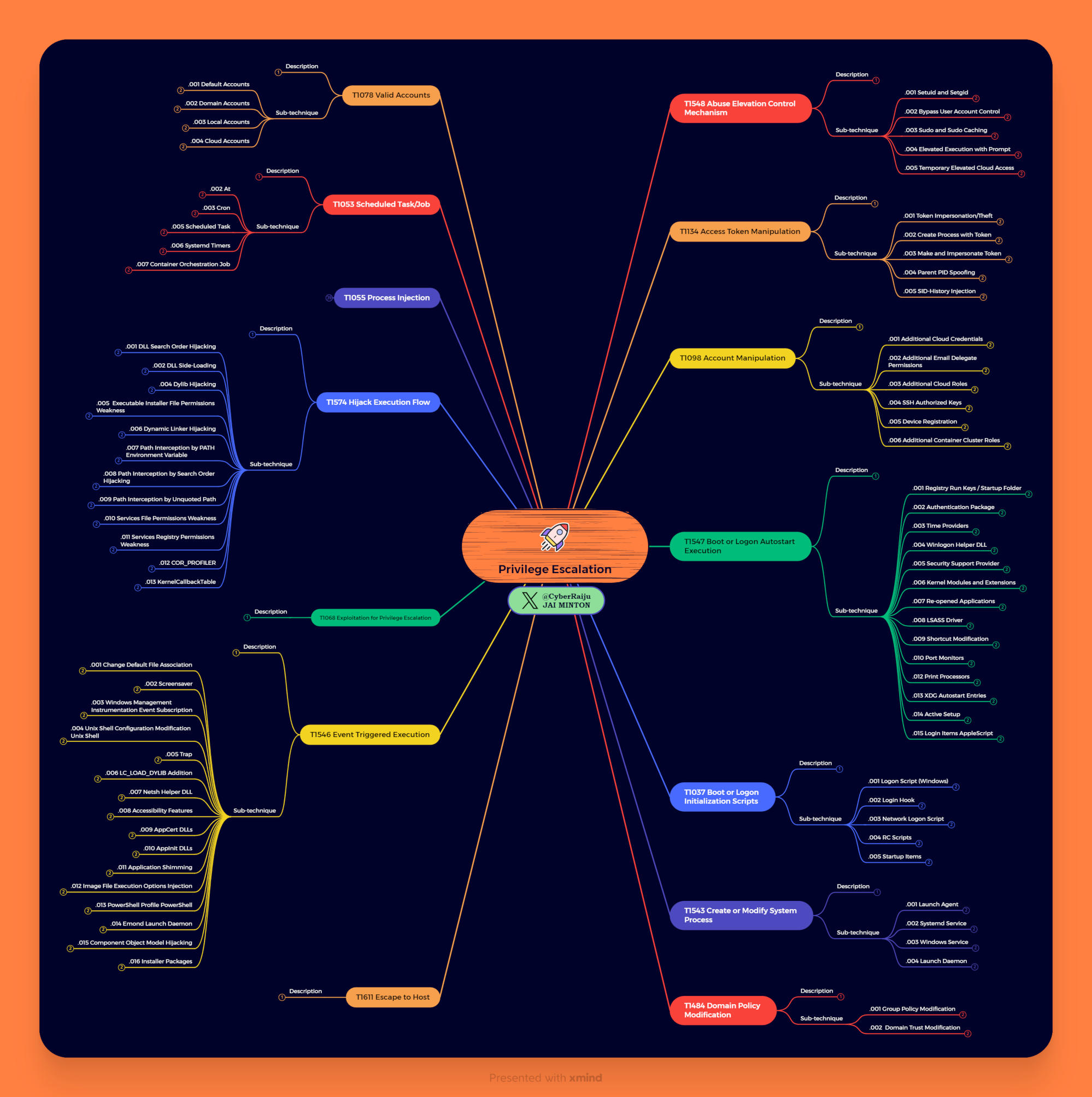
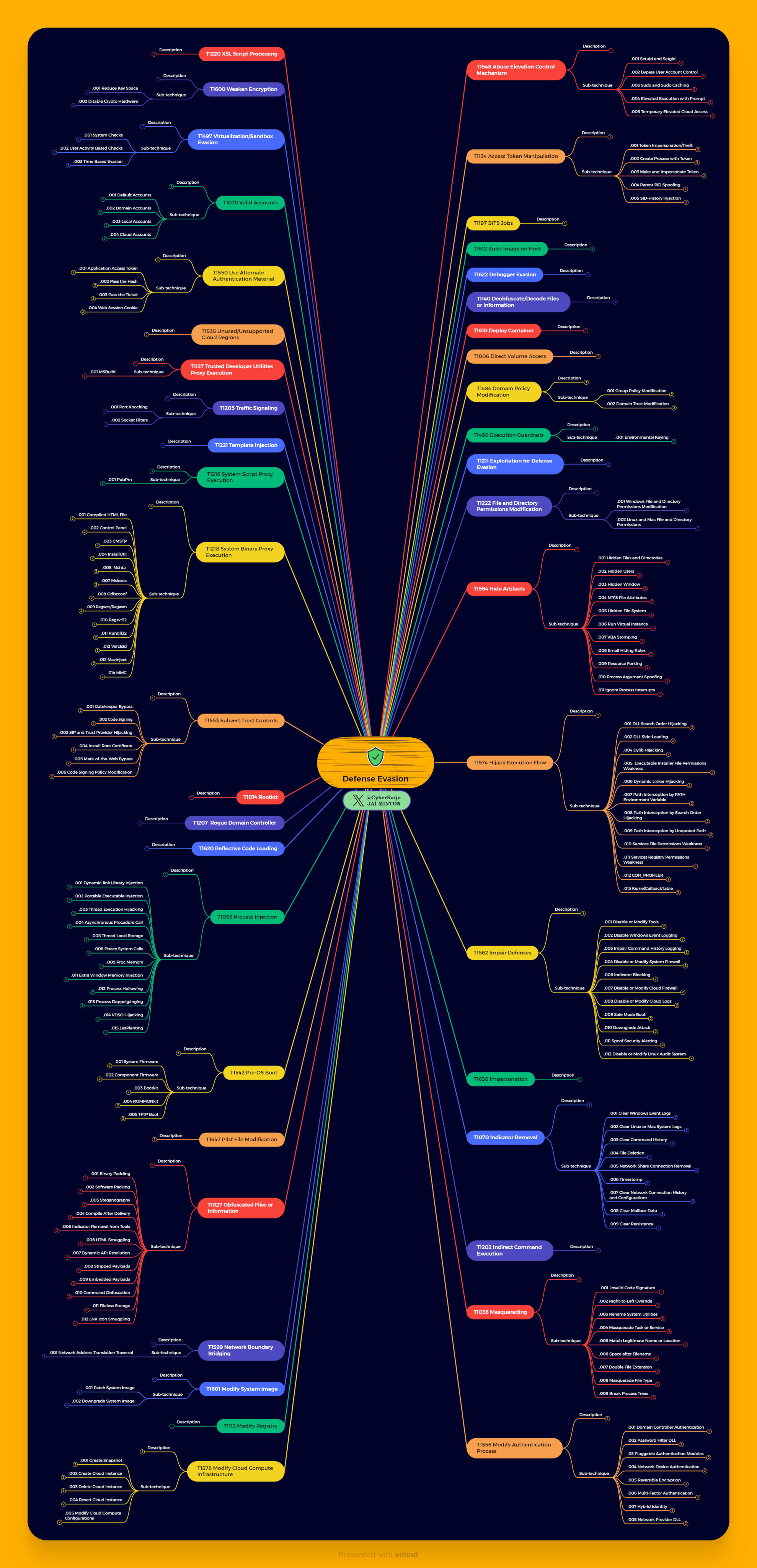
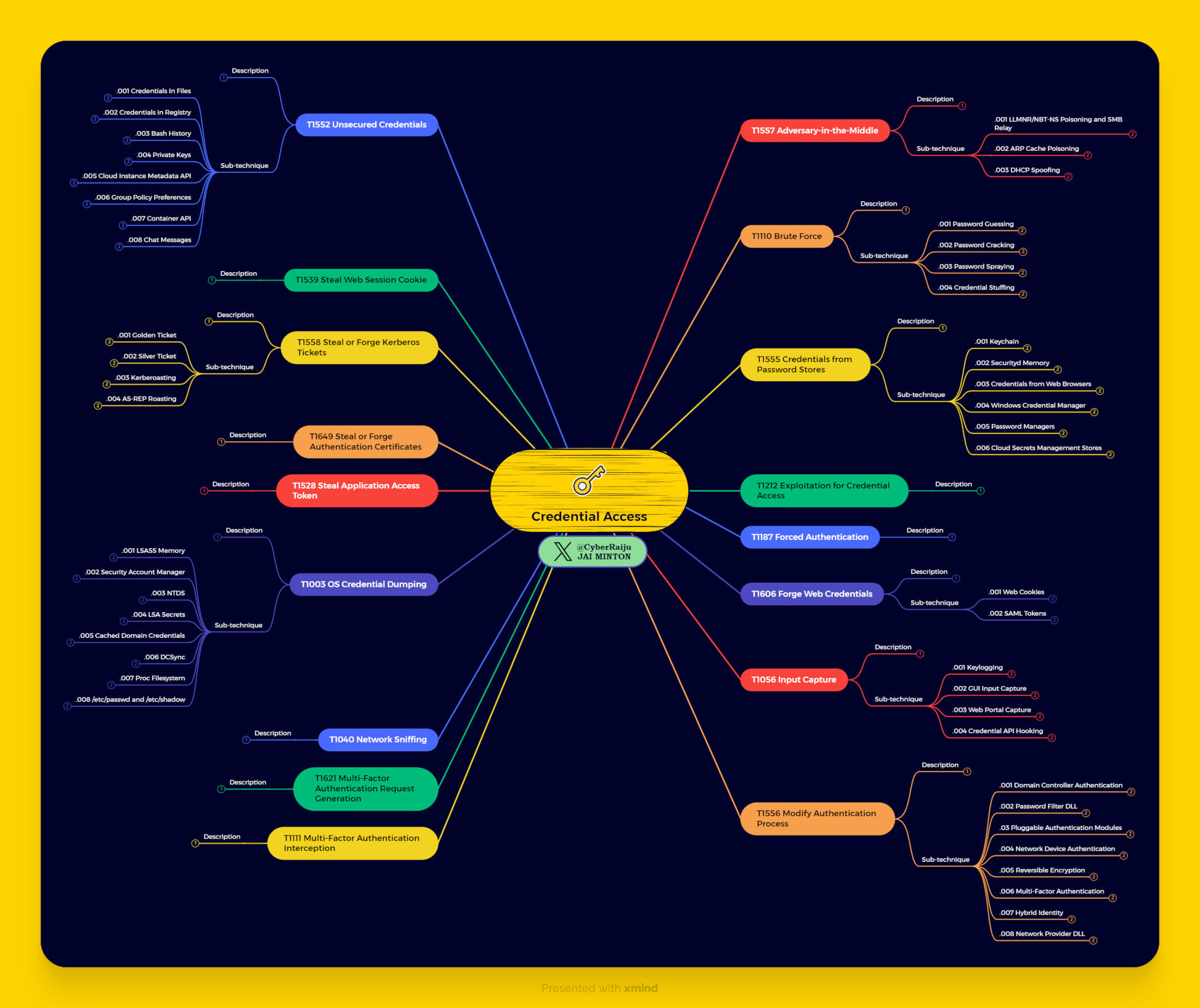
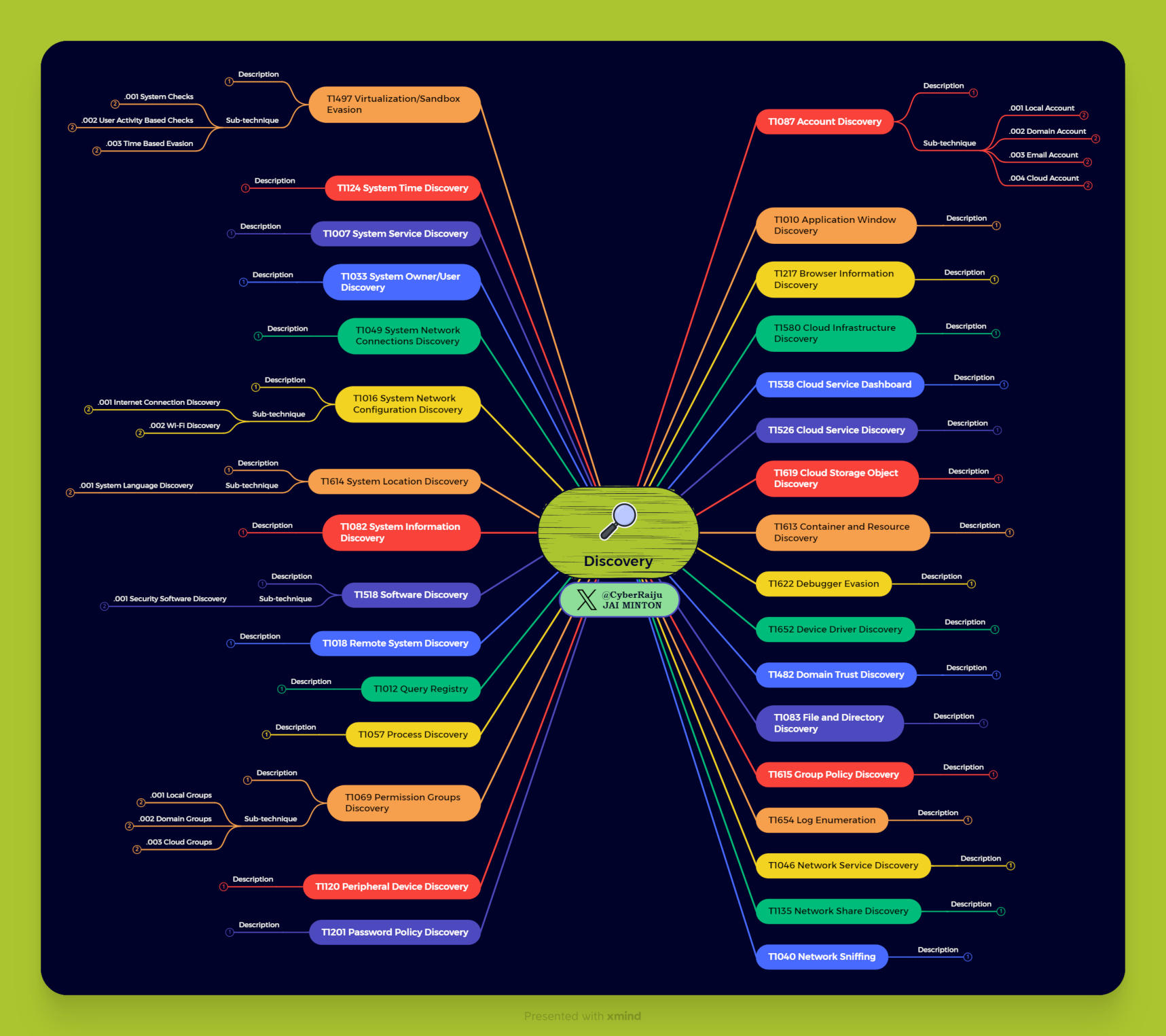
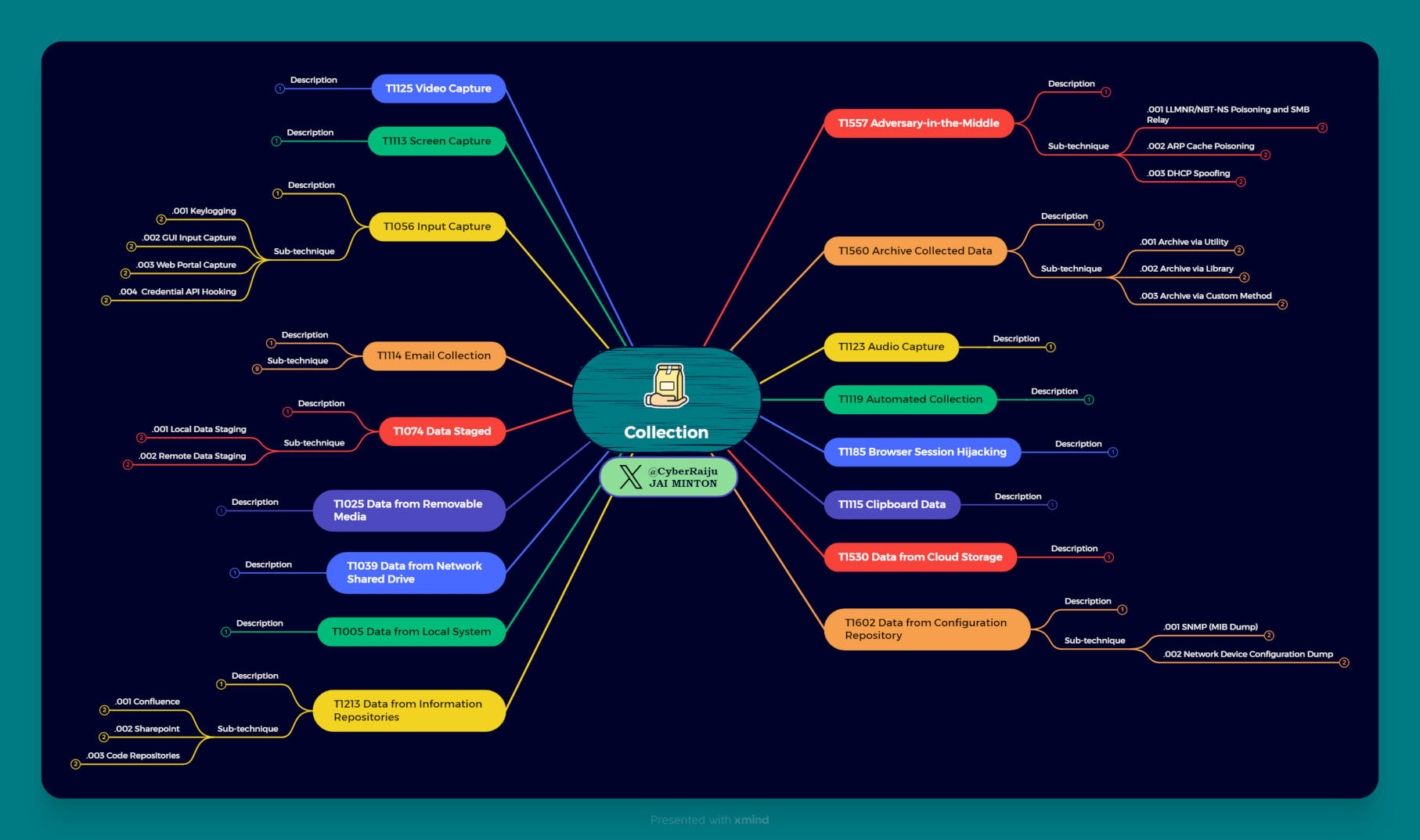
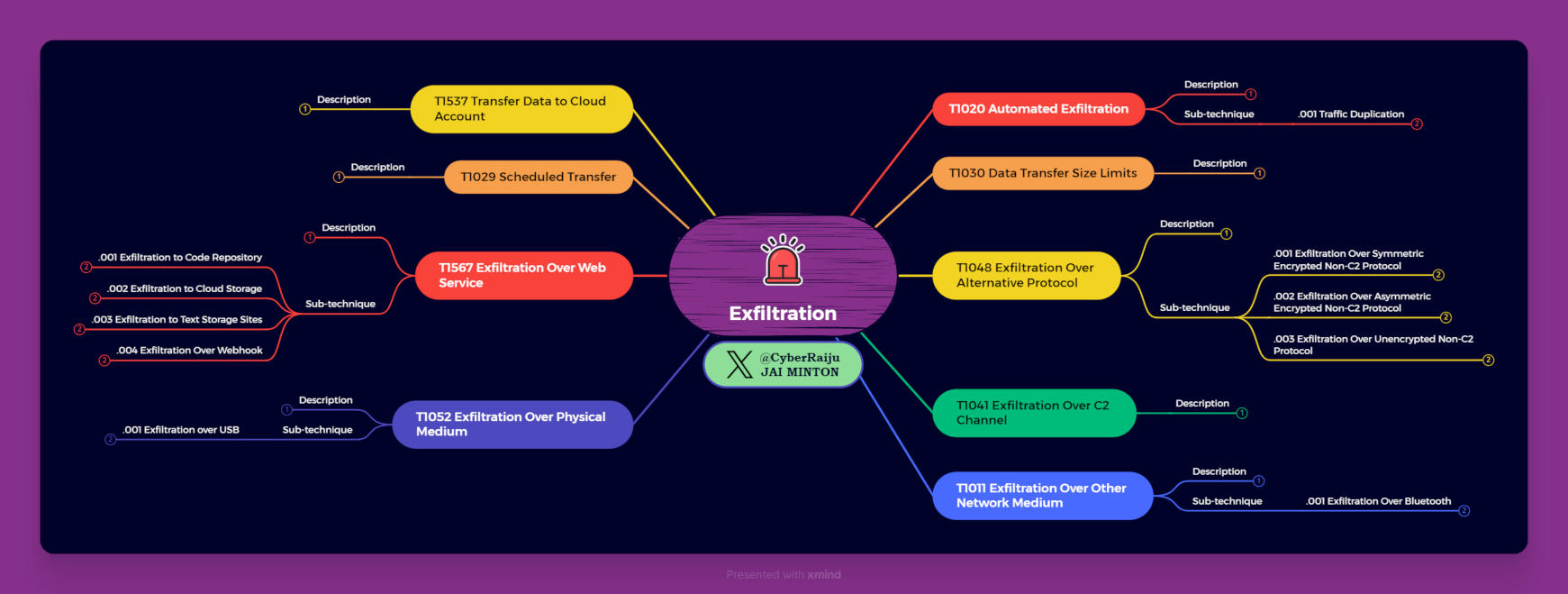
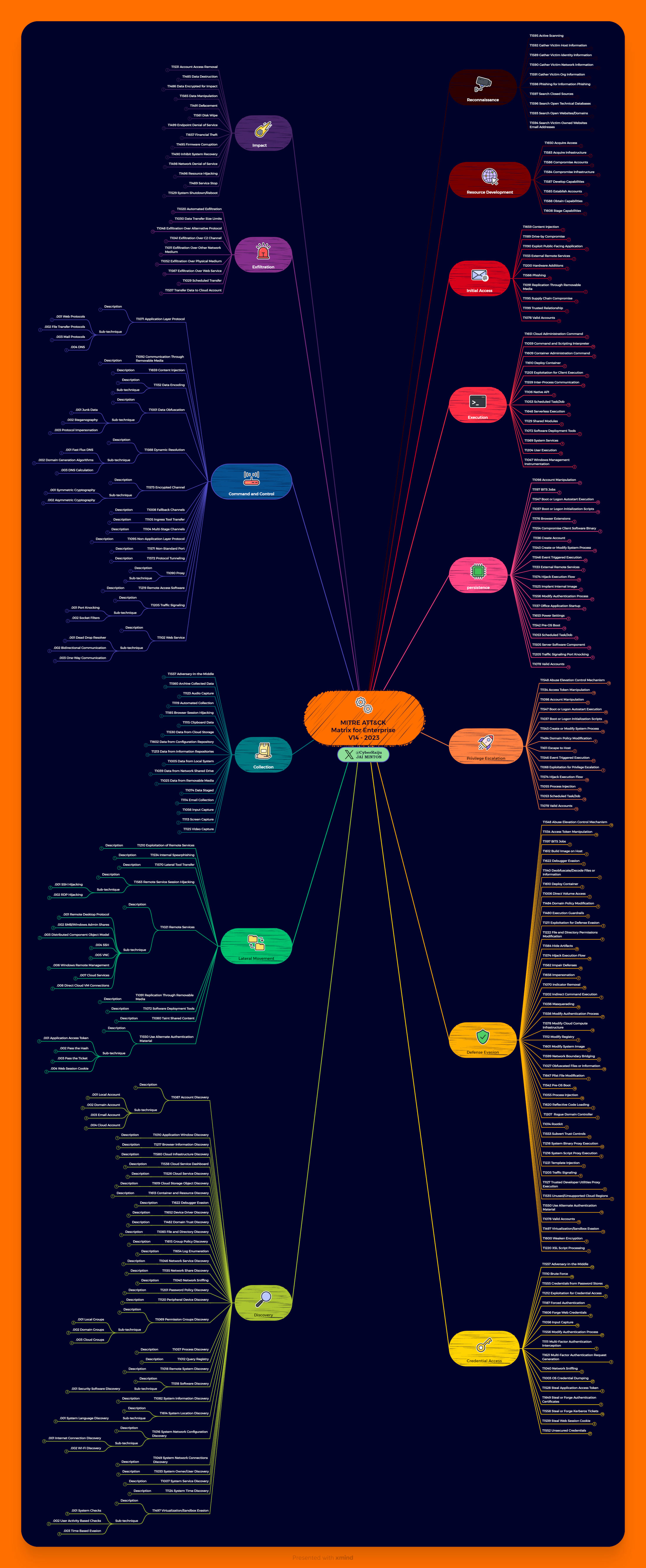
New: V14 MITRE ATT&CK Mind Maps
Get high quality versions on Github.
These use Olaf Hartong’s ‘ATT&CK Rainbow of Tactics’ as a basis for colour schema.
Bonus Initial Access Infographic

Joining in - MITRE ATT&CK Wheel of Fortune
For those wishing to have some fun and learn, I’ve created a spreadsheet that can be used to randomly generate a number for ‘Enterprise’, ‘Mobile’, or ‘Pre-Attack’ methods as outlined by the MITRE Corporation. This can also be used to link directly to the MITRE documentation, challenge yourself, and keep track of your progress. I’ve included a download link below (this uses no macros, only the excel random formula, and as such you will need to enable editing to refresh the number cells and ‘spin the wheel’).